Table of Contents
At 2:47 AM, Sarah got the alert every security leader dreads: "Critical: Unusual file activity detected."
Within minutes, 12,000 files were encrypted across her fintech’s network in Bangalore. By sunrise, the board had five questions. They had zero answers.
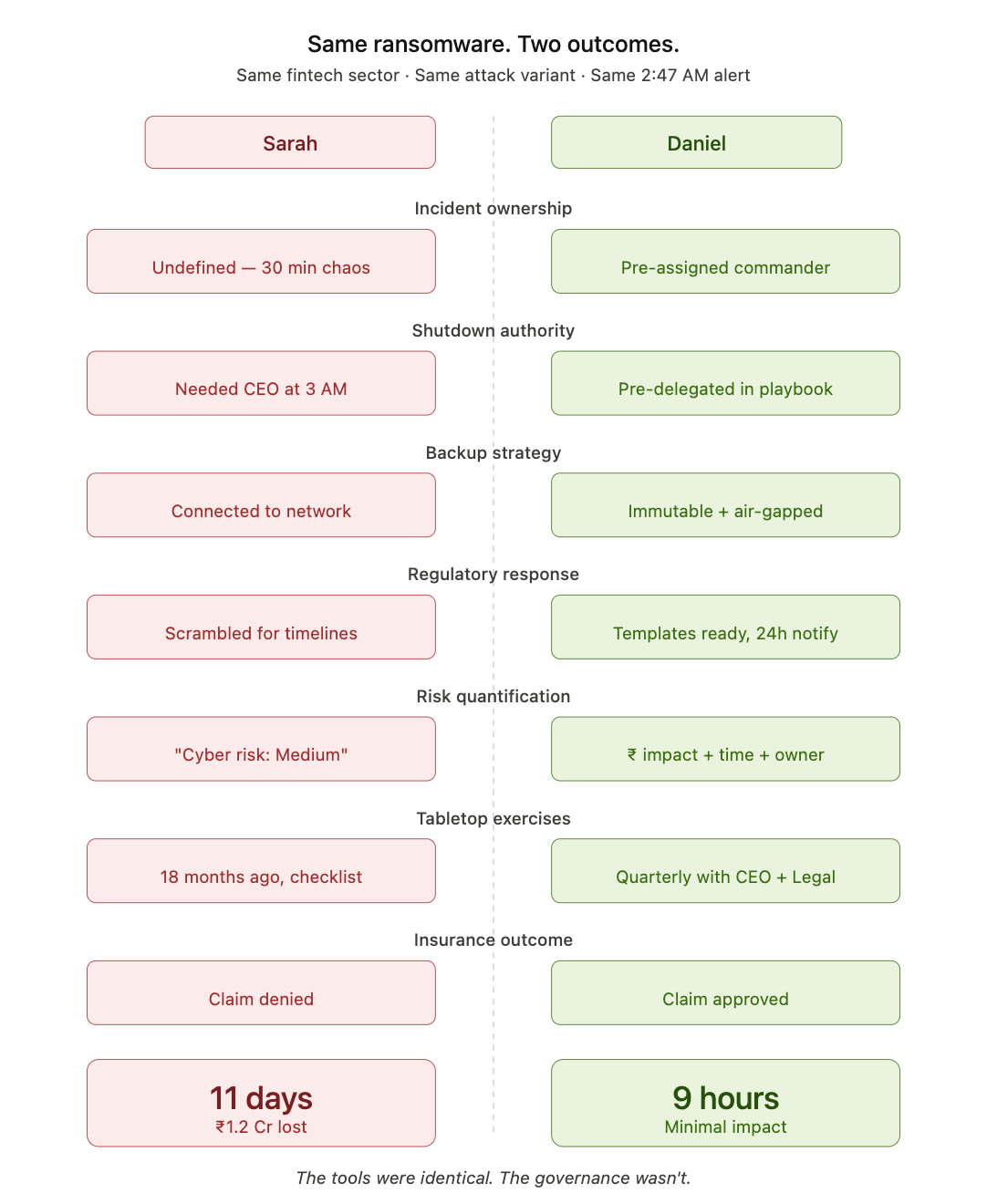
The result: 11 days of downtime. ₹1.2 crore in lost revenue. Insurance claim denied.
Denied, not because controls were missing, but because nobody could prove they existed.
How a Combat Leader Approaches a Ransomware Incident
Daniel led security at a similar fintech. Same attack. Same ransomware variant.
Recovery time: 9 hours.
He didn't have better tools. He had made one category of decision differently, he'd operationalized his GRC before the crisis.
Authority was pre-assigned. Tabletops ran quarterly with the CEO and legal in the room. Backups were immutable, air-gapped, and restore-tested at six hours. Risk entries carried rupee figures, not color codes. CERT-In notification templates were ready to send.
When the same 2:47 AM alert hit, nobody asked "who decides?" they already knew.
Now Read Those Five Questions.

Not as Sarah's problem. As yours.
If your 2:47 AM alert hits tonight — do you have answers for all five? Not in theory. Not in a policy PDF nobody's opened since the last audit. Answers that someone can act on in the first 30 minutes.
If even one is unclear, you're not under-tooled. You're under-governed.
Sarah and Daniel had the same EDR, the same firewalls, the same antivirus. The gap wasn't technology. It was whether decisions had been made before they were needed.
Security tools detect attacks. GRC determines whether you survive them.
Share your thoughts with me using the links below.
- M D Sathees Kumar ( Book a Quick Connect on my Cal.com )
Linkedin - https://www.linkedin.com/in/mdsathees/
Stay Ahead in GRC
Never miss an update in the Governance, Risk, and Compliance (GRC) domain. Follow below newsletter to get expert insights, trends, and actionable strategies delivered straight to your inbox.
👉 Check out the featured newsletter below:




