CISO's phone buzzes
The Future Arrived at 3:47 AM
Picture this: It's 3:47 AM. Your CISO's phone buzzes. Not with an alert about a breach but with a notification that a misconfigured cloud bucket was detected, analyzed, and automatically remediated. By the time she checks her phone at 6:30 AM, the incident report is already filed, the root cause documented, and the control gap closed.
This isn't science fiction. It's Tuesday.
Welcome to the audit-every-minute revolution where compliance happens in the background, like breathing, and the annual audit scramble becomes a relic of a slower, more dangerous era.
The $4.45 Million Question
Here's a number that should make every executive pause: $4.45 million [fortifydata.com]. That's the average cost of a single data breach in 2023.
But here's the twist: organizations aren't losing sleep over the breaches that happened. They're terrified of the ones they don't know about yet.
Between 2021 and 2023, 2.6 billion personal records were compromised [scrut.io]. Read that again—not million, billion. And 80% of those violations involved data stored in the cloud [scrut.io], the same infrastructure we've all rushed to embrace.
Meanwhile, regulatory penalties are escalating. One major organization recently paid $1.5 million [scrut.io] for a compliance lapse discovered in February 2025. Not for a breach. Just for failing to maintain proper controls.
The message is clear: The cost of not knowing is now higher than the cost of knowing.
The Illusion of the Annual Audit
For decades, we've treated compliance like a dental checkup something you do once a year, maybe twice if you're diligent. You gather evidence, prepare documentation, hold your breath during the auditor's visit, and then... relax for another 12 months.
But here's what's happening in those 12 months:
Your cloud infrastructure changes 847 times
New applications are deployed without security reviews
Third-party vendors experience breaches you don't hear about for weeks
Employee credentials are compromised and sold on the dark web
Regulatory frameworks evolve, and you're still compliant with last year's version
It's like checking your car's brakes once a year and hoping nothing goes wrong during the other 364 days. Except in compliance, something is always going wrong.
The Wake-Up Call: When 91% Isn't Enough
Here's a statistic that reveals both the problem and the opportunity: 91% of companies plan to implement continuous compliance within the next five years [fortifydata.com].
Impressive, right? Until you hear the next number: Only 5% have actually done it [fortifydata.com].
That 86-point gap? That's where the revolution is happening. That's where competitive advantage is being built. That's where the future of compliance is being written not by compliance officers, but by CTOs who understand that security and operations are no longer separate concerns.
Among those who've made the leap, the results are striking. 94.2% of security leaders report that continuous controls monitoring doesn't just improve compliance it fundamentally transforms security posture.
They're not monitoring more. They're worrying less.
The Anatomy of Real-Time Compliance
So what does audit-every-minute actually look like? Let's follow the journey of a single configuration change:
11:23 AM – A developer deploys new code to production
11:23:15 AM – Automated scanners detect the change
11:23:47 AM – AI analyzes the change against 847 control requirements across six frameworks
11:24:03 AM – A potential GDPR violation is flagged
11:24:18 AM – Relevant stakeholders receive contextualized alerts
11:26:42 AM – The developer receives specific remediation guidance
11:31:09 AM – Issue resolved, documentation updated, audit trail complete
Total time: 8 minutes, 9 seconds.
In the old model, this violation might have been discovered months later during an audit, resulting in emergency fixes, documentation scrambles, and potential regulatory exposure.
Now? It's just another Tuesday morning.
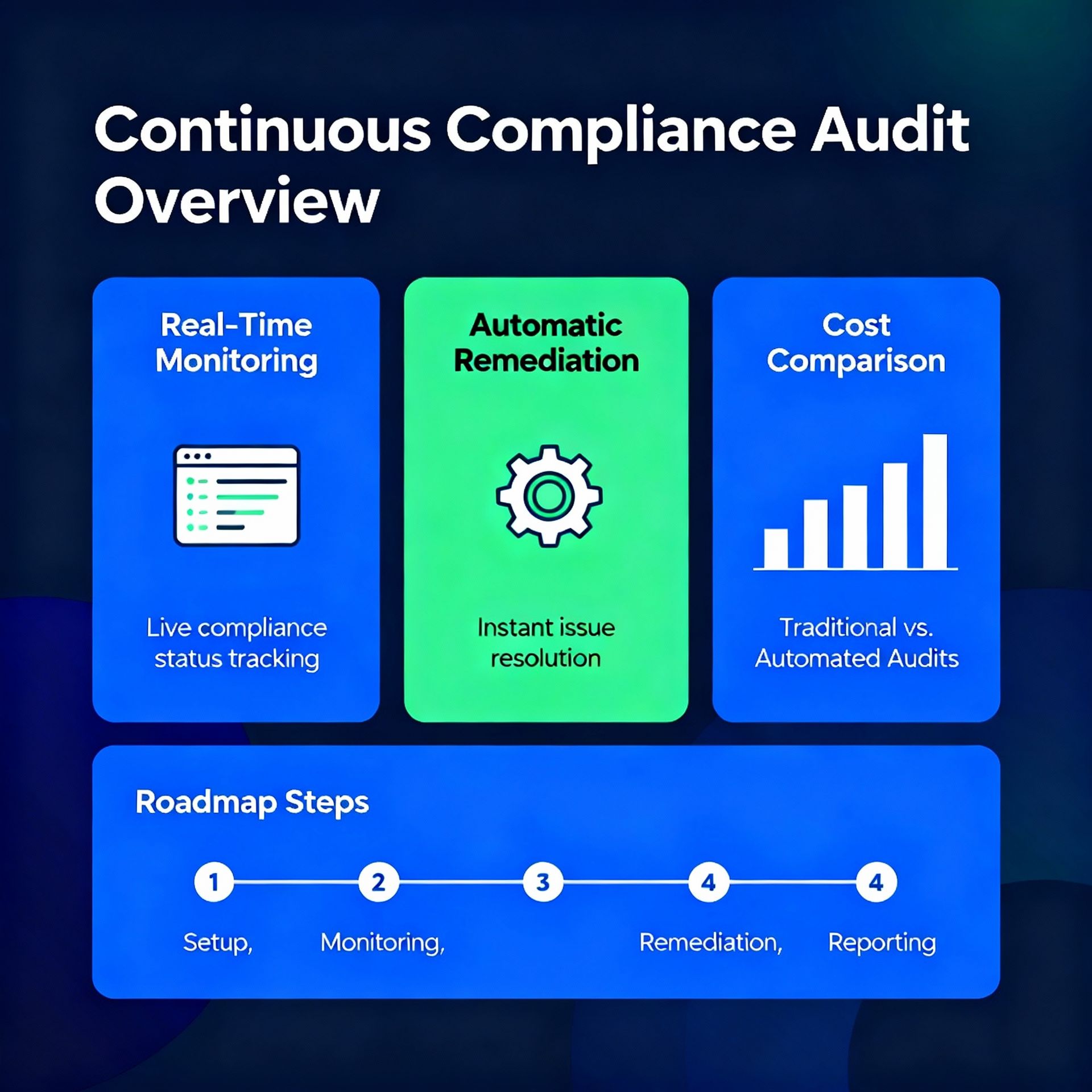
The Three Pillars of Continuous Compliance
Pillar One: Everything Leaves a Trail
Modern compliance platforms don't ask for evidence—they collect it. Continuously.
Every log entry. Every configuration change. Every access request. Every third-party integration. It's all captured, timestamped, and mapped to relevant controls.
The result? When auditors arrive, you don't prepare for them. You simply give them access to the system and watch as they conduct a real-time review of your actual security posture, not a carefully curated snapshot from three months ago.
Pillar Two: Intelligence That Never Sleeps
This is where AI transforms from buzzword to business advantage.
These systems don't just collect data—they understand it. They know that 100 failed login attempts from the same IP address matters more than 10,000 successful ones. They recognize when a vendor's security posture degrades before it makes the news. They forecast compliance gaps based on upcoming regulatory changes.
They operate 24/7/365, processing millions of events, learning patterns, predicting risks—and they never need coffee.
Pillar Three: Action Without Friction
Here's the real magic: these systems don't just detect problems. They often fix them.
Misconfigured bucket? Remediated automatically.
Expired certificate? Renewed and documented.
Control deviation? Corrected and recorded.
The humans? They're notified, certainly. But they're not scrambling. They're reviewing, approving, learning—operating at a strategic level instead of a tactical one.
The Hidden Cost of Waiting
Let's talk about what continuous compliance really costs and what it saves.
The Investment:
Platform licenses and integration work
Training teams to work in a continuous model
Cultural change (the hardest part, always)
The Return:
Consider the math: preventing just one major breach pays for years of continuous monitoring. Avoiding one regulatory penalty funds the entire program. But the real savings are harder to quantify and far more valuable:
Time recovered: Teams spending hours on strategic work instead of evidence gathering
Risk reduced: Vulnerabilities measured in minutes, not months
Innovation accelerated: Compliance baked into deployment, not bolted on after
Sleep improved: Yes, this matters
One security leader put it perfectly: "We went from asking 'Are we compliant?' to knowing 'We are compliant.' That's not just a reporting improvement—it's a fundamental shift in organizational confidence."
The Roadblocks Nobody Talks About
But let's be honest: this transformation isn't easy.
The Cultural Challenge: Teams resist constant monitoring. "I'm not being micromanaged by a dashboard" is a real sentiment that requires real leadership to address.
The Skill Gap: Continuous compliance requires people who understand both security and data analytics. That's not a common combination, and training takes time.
The Integration Nightmare: Your compliance data lives in 47 different systems. Getting them to talk to each other? That's where consultants make their money.
The Regulatory Chaos: Thirty-two percent of compliance professionals cite regulatory change as their top challenge [fortifydata.com]. Frameworks evolve constantly, and keeping up feels like running on a treadmill that's speeding up.
The Alert Fatigue: Without proper tuning, continuous monitoring can drown teams in notifications. The difference between signal and noise isn't technical—it's strategic.
What Happens Next: Five Predictions
Prediction 1: Regulators Will Demand It
Within three years, major frameworks will begin requiring continuous monitoring for critical controls. The annual audit won't disappear, but it will become a validation exercise, not a discovery process.
Prediction 2: Auditors Will Become Consultants
When evidence collection is automated, auditors shift from checklist executors to strategic advisors. They'll focus on risk patterns, control optimization, and emerging threats—work that requires judgment, not just documentation review.
Prediction 3: Compliance Becomes Invisible
The best compliance programs will be the ones nobody thinks about. Controls will be embedded so deeply into operations that teams won't distinguish between "doing the work" and "being compliant." They'll be the same thing.
Prediction 4: AI Will Write the Policies
Generative AI will monitor regulatory changes, update policy language, generate control documentation, and even suggest new controls based on emerging risks. Compliance teams will shift from writers to editors.
Prediction 5: Real-Time Will Become Real-Time
Today's "continuous" monitoring still operates in minutes or hours. Tomorrow's systems will operate in seconds, with predictive capabilities that prevent issues before they occur.
The Choice Before You
Here's the uncomfortable truth: every day you wait to implement continuous compliance, the gap between your organization and your competitors widens.
This isn't about being an early adopter. With 91% of companies planning implementation within five years [fortifydata.com], this is about being in the first wave versus the last.
The organizations moving now aren't just avoiding penalties and preventing breaches. They're building something more valuable: institutional confidence. The ability to say "we know" instead of "we think." The freedom to innovate without fear. The competitive advantage of moving at machine speed while maintaining human oversight.
The Last Audit
Imagine the annual audit of 2030.
The auditors arrive. You provide system access. They review real-time dashboards showing 365 days of continuous control monitoring, automated remediation, and risk analytics. They spot-check a few items. They nod. They leave.
The entire process takes four hours instead of four weeks.
Your team doesn't scramble. They barely notice.
Because in your organization, every minute is audit-ready. Every day is compliant. Every risk is monitored.
The audit-every-minute revolution isn't coming. It's here.
The only question is: are you ready to stop checking your brakes once a year and start building a car that monitors them continuously?
Your competitors already know the answer.
Getting Started: A Practical Path Forward
If you're ready to move beyond annual compliance theater, here's where to begin:
Week 1-2: Assess your current state honestly. Map where compliance data lives today and identify your highest-risk areas.
Week 3-4: Define what "continuous" means for your organization. Real-time analytics? Hourly monitoring? Daily reporting? Be specific.
Month 2: Select technology partners. Look for platforms that integrate with your existing stack, not ones that require wholesale replacement.
Month 3-4: Start small with high-value controls. Pick one framework, one critical system, and prove the model works.
Month 5-6: Expand coverage systematically. Let success build momentum.
Month 7-12: Embed continuous compliance into culture. Celebrate early wins. Share dashboards. Make compliance visible and valuable.
Year 2: Scale across frameworks, systems, and geographies. Automate remediation. Train teams. Optimize signal-to-noise.
Year 3: Export your model. Extend monitoring to vendors. Build predictive capabilities. Become the organization others benchmark against.
The journey from annual audits to continuous compliance isn't a sprint. It's a transformation.
But every transformation begins with a single decision.
What will yours be?
Every control tells a story. Share yours and continue the dialogue with me on LinkedIn.
Stay Ahead in GRC
Never miss an update in the Governance, Risk, and Compliance (GRC) domain. Follow below newsletter to get expert insights, trends, and actionable strategies delivered straight to your inbox.
👉 Check out the featured newsletter below:





